A detailed report on how reckless social media disclosures of sensitive US Intelligence Surveillance and Reconnaissance ISR flight paths over the Lake Chad region compromised counter-terrorism efforts and forced ISWAP fighters to tactically reposition .
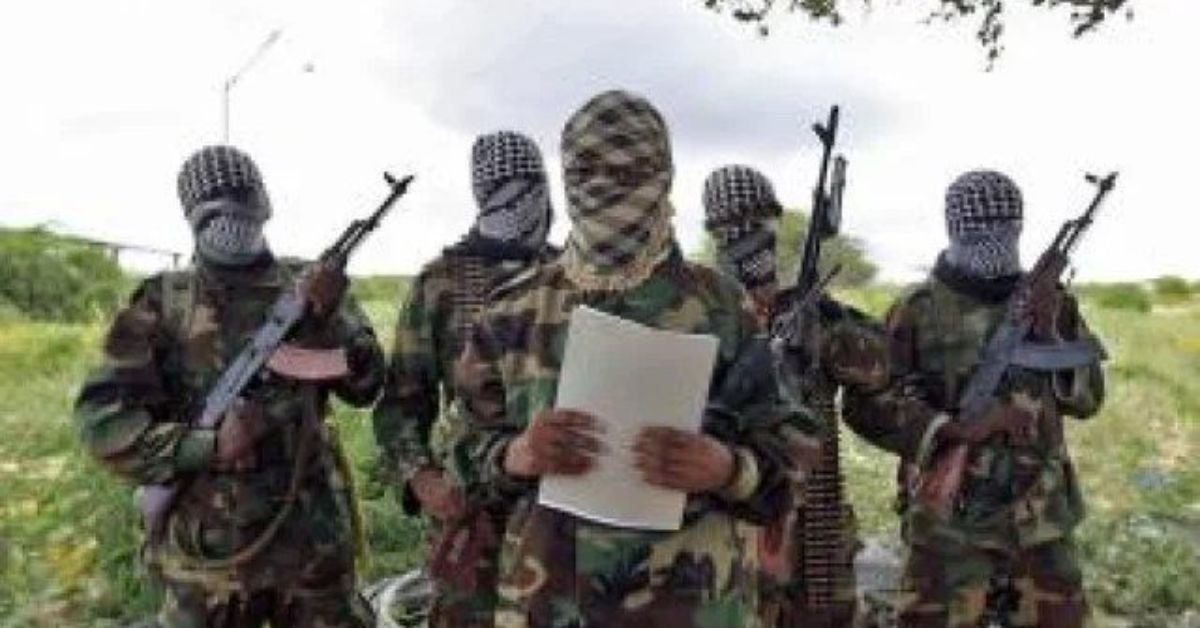
The protracted and complex counter-insurgency operations against the Islamic State West Africa Province ISWAP in Nigerias volatile Lake Chad Basin have faced a critical and unforeseen setback the reckless disclosure of sensitive military intelligence on social media platforms Recent reports from security sources indicate that a series of public posts detailing the real-time flight paths of covert US Intelligence Surveillance and Reconnaissance ISR aircraft compromised the missions forcing ISWAP fighters to rapidly abandon monitored locations and tactically relocate .
This incident underscores the perilous intersection of open-source information digital tracking and asymmetric warfare highlighting a major operational vulnerability for both Nigerian and partner forces .
The Covert Surveillance Mission Exposed
The core of the issue involves US Air Force ISR aircraft conducting crucial surveillance missions over ISWAP strongholds in the Lake Chad region specifically Northern Borno State Nigeria These flights which were reportedly part of an agreement between the US and Nigerian governments to fill ISR gaps were intended to remain highly covert The surveillance aimed to gather intelligence on ISWAPs movements command structure and potential target areas for future counter-terrorism operations or potential air interdiction .
Also Read : Aisha Yesufu Blasts Nigerian Legislature Calls Them Rubber Stamp Demands Shame
The aircraft in question was tracked taking off from Accra Ghana and was seen circling key ISWAP areas including its supposed Mantiqah Krinwa Multiple sorties had been flown over consecutive days building a pattern of surveillance data crucial for military planning .
The Social Media Compromise
The operational security of these missions was disastrously undermined by a social media handler—specifically identified as a security expert and tracker—who began posting real-time flight paths and details of the ISR operations on platforms like Twitter X These posts intended for open-source intelligence OSINT enthusiasts or general public knowledge inadvertently became a critical immediate and free intelligence feed for the terrorist group .
Security sources confirmed that ISWAP actively monitors these public platforms enabling them to gain instantaneous awareness of the surveillance A highly sensitive military operation designed to catch the terrorists unawares was thus compromised in the span of a few digital posts .
People on social media must understand that sharing operational intelligence especially in real time is not content it is sabotage Terrorists monitor these platforms too noted a security source .
ISWAPs Tactical Relocation
The immediate and most damaging consequence of the leak was the tactical repositioning of ISWAP fighters Upon realizing they were under active US surveillance the group quickly initiated movements to avoid potential strikes .
- Initial Target Area The ISR flights were focused on locations like Mantiqah Krinwa .
- The Relocation The security leaks unsettled the group prompting a tactical movement from Dogon Chikun to Bulabulin in an apparent attempt to avoid potential air interdiction in identified locations .
While the group may not have been heavily concentrated in the area initially monitored the mere fact that they were forced to move indicates that the intelligence mission was effective in causing disruption However the subsequent leak negated any potential for an intelligence-driven air interdiction allowing the fighters to escape without penalty This action not only preserves their fighting strength but also forces security forces to expend more time and resources to locate them again .
The Broader Security Implications
This incident carries profound implications for counter-terrorism efforts in the Lake Chad region .
- Direct Operational Endangerment The leaks directly compromise ongoing operations endanger the lives of personnel involved in the surveillance and subsequent follow-up missions and undermine the strategic cooperation between Nigerian and US forces .
- Empowerment of Terrorist Networks The ability of ISWAP to rapidly adapt and evade surveillance due to leaked information hands them a significant tactical advantage demonstrating that they can leverage modern communication channels as effectively as their military opponents .
- The OSINT Dilemma The incident highlights the growing dilemma posed by open-source intelligence While OSINT can be a powerful tool for journalists and researchers the line between informative tracking and jeopardizing military operations is thin and often crossed without malicious intent but with devastating results .
- Strategic Vulnerability For the Nigerian military and its partners this exposure reveals a major vulnerability in information control It necessitates a new strategy for managing operational details especially in an era where civilian flight tracking sites and social media are pervasive .
The future of counter-terrorism in this theatre must now account for this digital battleground Security experts and officials have called for greater restraint from social media users bloggers and open-source enthusiasts urging them to avoid amplifying sensitive operational intelligence that can inadvertently bolster terrorist networks The reckless act of real-time disclosure has allowed ISWAP to maintain its operational rhythm and demonstrates that in the modern conflict zone a simple post can be as damaging as enemy fire .
Dynamic Disclaimer
Disclaimer The news information presented here is based on available reports and reliable sources concerning military and security operations in the Lake Chad region Readers should cross-check updates and official statements from official news outlets and government bodies for the most current information .